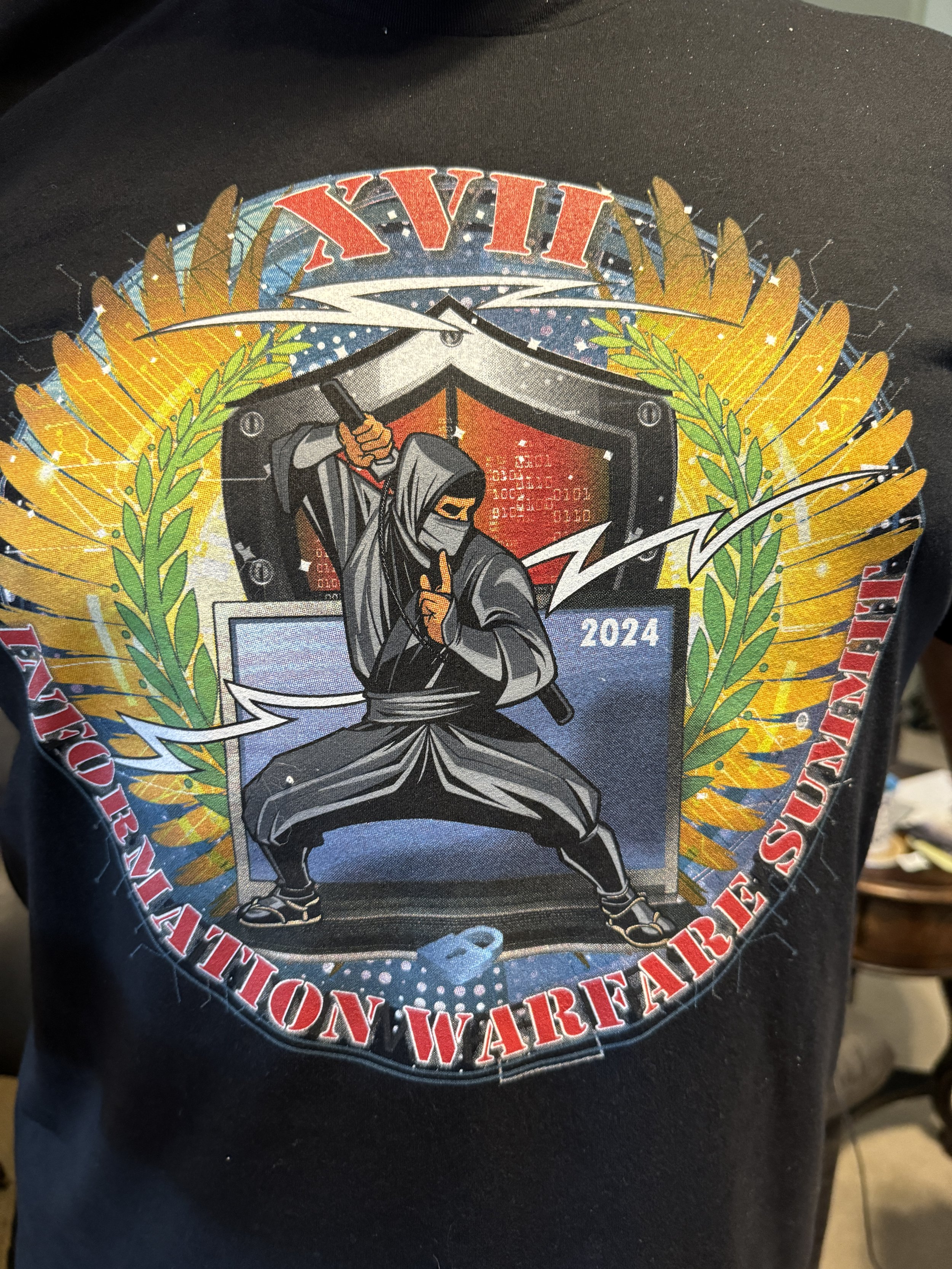
Information Warfare Summit 2026
AI-POCOLYPSE?
The Unwritten Future
Wednesday
October 7, 2026
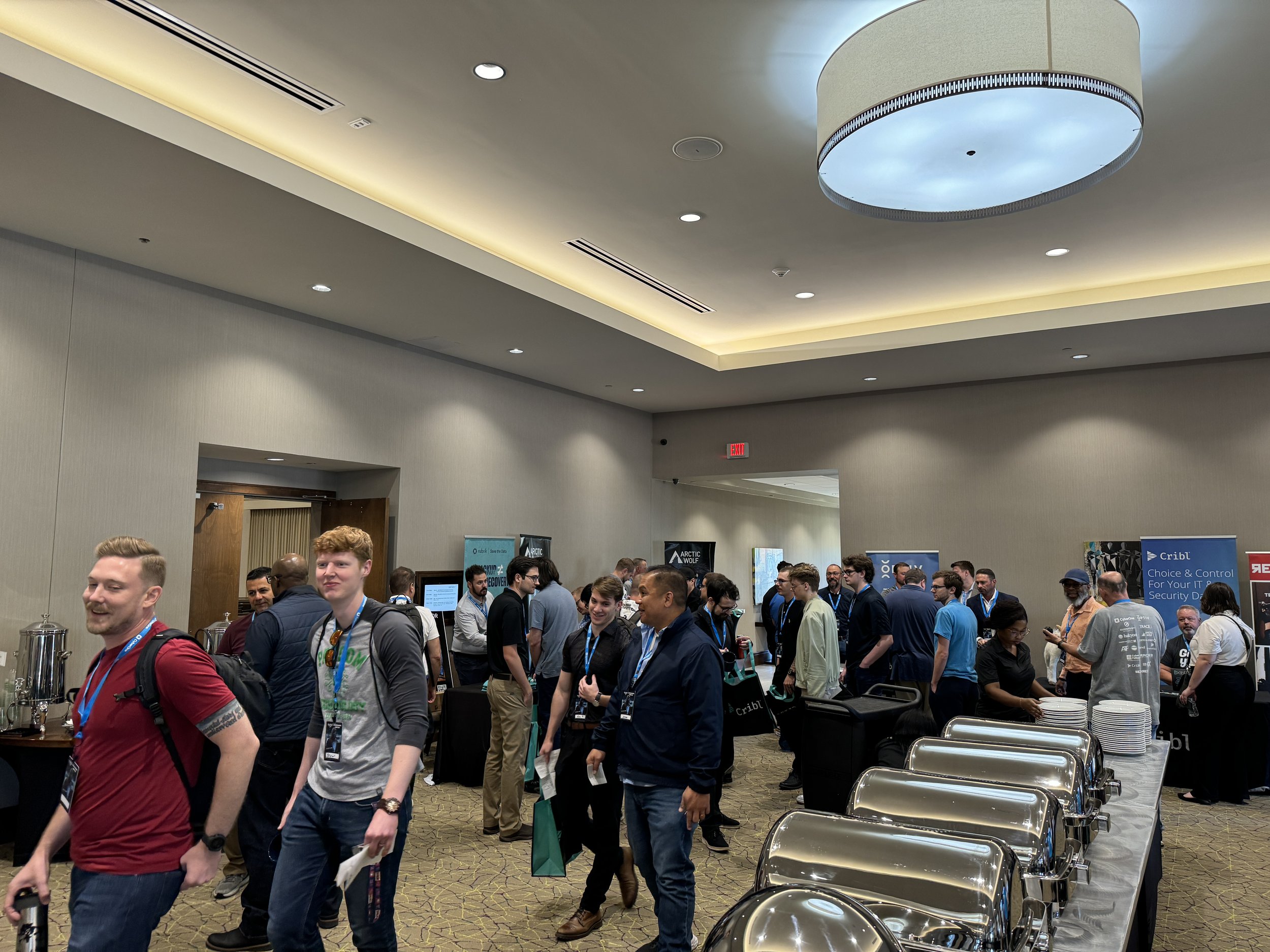
Edmond Conference Center
2833 Conference Drive, Edmond, OK 73034
-
April 1 - May 31 - $35
-
June 1 - August 31 - $45
-
September 1 - October 9 - $65
-
February 1 - March 31 - $25
Download the Mobile App to have event details at your fingertips!
Scan in to sessions for CPE tracking
Bookmark the sessions the you'd like to attend
Access speaker profiles
Connect with sponsors
Click here to download the Eventzilla mobile app! (Mobile Only)